All about malware
As you know, every year there is a medical campaign for influenza vaccination. This is because influenza outbreaks are usually seasonal – the disease comes to light at certain times of the year and begins to spread, affecting more and more people.
The activity of viruses that attack PCs, smartphones, tablets and enterprise networks is seasonally independent and cannot be predicted. The “computer flu” epidemic never ends. Yes, because of it users do not suffer from chills or pain in the whole body, but they are not given rest symptoms caused by other kinds of attack – malware.
Malware falls out of the horn of plenty, using a variety of attack methods, from subtle and sophisticated to simple and straightforward like scrap. But knowledge is power. Armed with the right information, you can reduce the risk of disease.
That’s why we offer you a short training course on malware to teach you what malware is, what its symptoms are, how it is infected, how to choose a cure and how to fight against future viruses.
What is malware?
Malware (or malware) is a collective term for malware or code that can cause damage to a computer system.
Malware is deliberately created hostile, intrusive and aggressive. It seeks to infiltrate, damage, partially take control of certain processes, or completely disable computers, computer systems, networks, tablets and mobile devices. Like human influenza virus, it interferes with normal operation.
The purpose of malware is to make illegal profits at your expense. Although malware cannot damage system hardware or network equipment (but even here we know the exception – we’ll talk about it below in the section on Google’s Android operating system), it can steal, encrypt or delete your data, change the functions of your computer or intercept control over it. It may also monitor your computer’s activity without your knowledge.
How do you know that the system is infected with malware?
Malware can manifest itself in many ways. Here are just some of the most common signs that indicate the presence of malware on your system:
- The computer starts to run slowly. One of the main consequences of malware infiltrating your operating system is to slow it down, whether you’re surfing the web or using local applications.
- The intrusive advertising starts to appear on the screen periodically. Unexpected pop-up ads are a typical sign of computer malware infection. They are most often caused by a specific form of malware – adware. Moreover, pop-up ads are usually associated with other hidden threats from malware. Therefore, it is important to remember: if the message “HEALTH! YOU WEARS FREE SEANCE OF PSICHICHICAL Reading!” Don’t click on it! No matter what prize the advertisement promises, you will still have to pay a lot of money.
- The computer often fails, hangs up, or displays a “blue death screen” that indicates a critical error on Windows systems.
- You notice that for unknown reasons the amount of free disk space has decreased. Perhaps you should blame it on the growing malware that is hiding somewhere on your hard drive.
- The Internet activity of the system has strangely increased.
- The intensity of system resources usage is too high, and the computer’s cooling fan is constantly running at full speed. This is a good sign that the malware is using system resources in the background.
- The home page of the browser has been changed without your permission. Clicking on a link takes you to unwanted web pages. This usually indicates that you clicked on the same “congratulations” pop-up message, after which unwanted software was installed on your computer. In similar cases, the browser can slow down considerably.
- New toolbars, extensions or plug-ins suddenly appear in the browser.
- The antivirus program stops working, you cannot update it, so you are left unprotected in the face of malicious software that disables it.
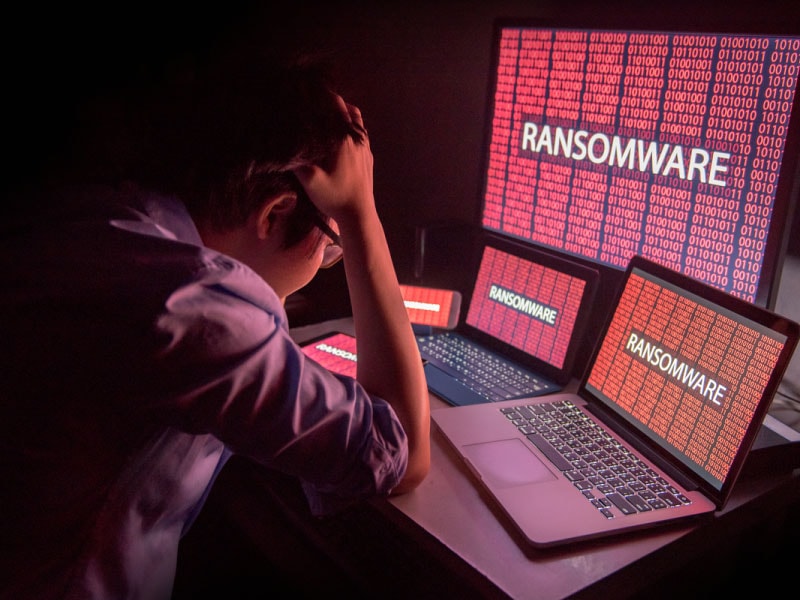
- There are also obvious virus attacks that do not even try to mask themselves. These tactics are chosen by ransomware: they declare themselves, report that they have stolen your data, and then demand a ransom for the return of files.
- And even if the system seems to be in order, it’s not a reason to be complacent, because the lack of news is not always good news. Dangerous malware can hide in the depths of your computer and do its dirty work without drawing attention to it: steal passwords, files with confidential data or use your computer to infect other computers.
How does it attack malware?
A malware attack can be carried out in many ways. The most common ways for malware to infiltrate the system are through the Internet and email. That is, it can happen at any time when you are working online.
Malware can infiltrate your computer when you (take a deep breath) browse hacked websites, open game demos, download infected music files, install new toolbars from an unknown vendor, download programs from untested sources, and open malicious email attachments.
In short, this can happen in any situation where you download content from the World Wide Web to a device that does not have a strong enough antivirus.
Malicious objects are often hidden in seemingly ordinary apps – and the likelihood of doing so increases when you download them from websites or messages rather than from a trusted app store. When installing applications, it is important to pay attention to warning messages, especially if they request permission to access your email or other personal information.
The best way to keep yourself safe is to install mobile apps only from trusted sources, trust only trusted third party app developers, and always download apps directly from the manufacturer’s website – and never from other websites.
Remember that cyberspace is full of cybercriminals and villains ready to bait you – offering you an “Internet Accelerator”, a new Download Manager, a program to clean your hard drive, or an alternative search service.
Malware’s insidious plans would not have been so successful without the most important component – you. They use your credulity, your habit of opening emails and moving on to attachments that only look harmless, they exploit your desire to click on a link and install a program that you can’t really trust.
It’s important to understand that we don’t want to embarrass you, because cybercriminals can outsmart even the most experienced users and make them install malware.
Even if you are installing the program from a reliable source, you may not notice that it asks for permission to install another application that you did not intend to install. This additional program is often disguised as an important component that it is often not.
Another method that uses social engineering resources has been observed by Malwarebytes experts in the UK. Attackers have attacked users with the direct payment feature of mobile devices.
While visiting certain websites, users inadvertently clicked on invisible buttons, after which the attackers, knowing the phone numbers of the victims, billed them directly through the mobile network and successfully debited funds in their favor.
Let’s be honest: a malware attack can be so sophisticated that it’s impossible to see it. It is likely that even a simple visit to a malicious website and viewing its page and/or banner will result in the shadow loading of unwanted objects.
On the other hand, if you do not use the proper security software, then malware infection and its consequences remain entirely on your conscience.
